In previous articles in this blog post series, I noted that even if advanced permissions options were a key reason behind SharePoint’s success, centralized, automatized permission management in SharePoint is virtually non-existent. There are two ways out of the permissions-management trap: writing PowerShell scripts or using third party products that can close the gap. This blog series focuses on SPDocKit, a tool that—IMHO—closes that gap in the best possible way. The second article in this series discussed batch permissions management using SPDocKit. This article will focus on managing permissions inside a single-site collection.
Part 1: SharePoint admin’s dream: Centralized permissions management
Part 2: Batch permissions management with SPDocKit
Part 3: On-the-fly permissions management with SPDocKit
Part 4: Permissions reporting and forensics with SPDocKit
SPDocKit’s Batch permissions management is very useful when dealing with a large number of site collections; it can be a real lifesaver in that scenario. However, administrators more often deal with permissions inside one site collection.
The SharePoint user interface gives us all the basic options for dealing with permissions. We can create, edit, and delete groups; manage group memberships; and create and manipulate permission levels. By drilling down through SharePoint securable objects (data structures), we can break and restore permissions and set specific permissions for all objects down to the item level.
Even though SharePoint offers many possibilities, much remains open. New sharing capabilities make it easier than ever before for users to break permissions on the item or folder level. It is not an easy task for administrators to identify those items. Cleaning up permissions remains a repetitive, slow task—moving users who obtained permissions directly to the appropriate SharePoint groups requires a lot of clicking. Administrators never get a broad overview of the situation with permissions at one particular site. Dealing with permissions and the entire user experience (or rather the “admin experience”) does not reach optimal efficiency. Thus, many SharePoint admins handle permissions exclusively through PowerShell. For those who are proficient in PowerShell, this is a legitimate alternative to the SharePoint UI. However, PowerShell is a command line tool and thus is not really appropriate for everyone, especially if all an administrator needs is to perform a few quick actions or get an overview of what is going with permissions on a particular site.
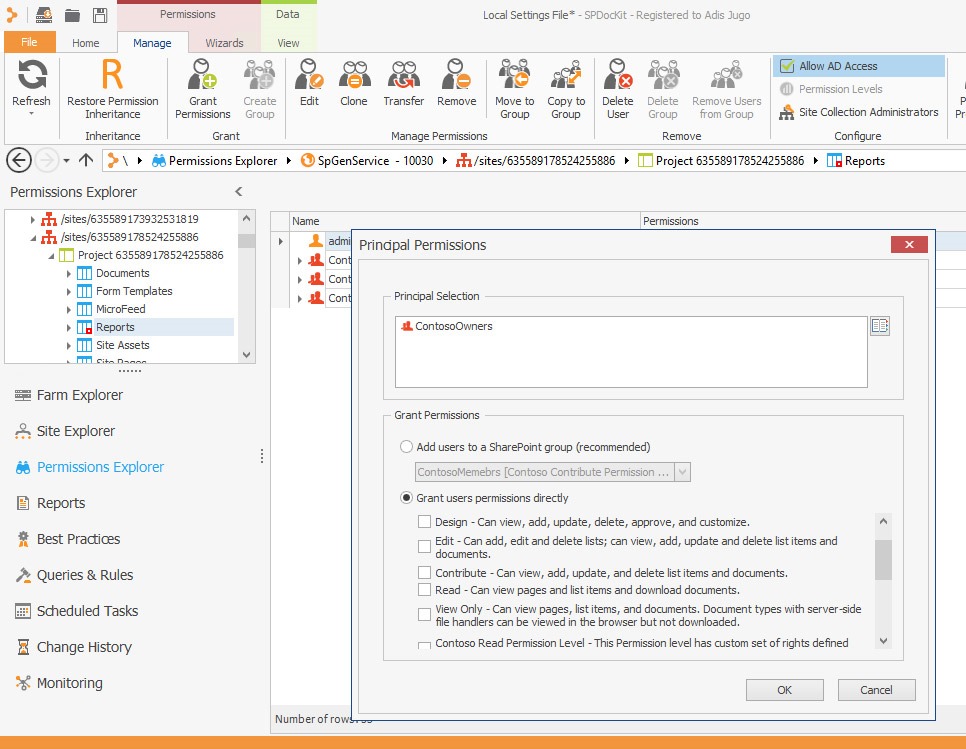
This is where SPDocKit comes in: in version 5, we got something called “Permissions Explorer.” Using a familiar, hierarchical tree view of SharePoint securable objects (data structures), administrators can drill down through the site collection objects to do everything SharePoint allows with permissions, and even a bit more.
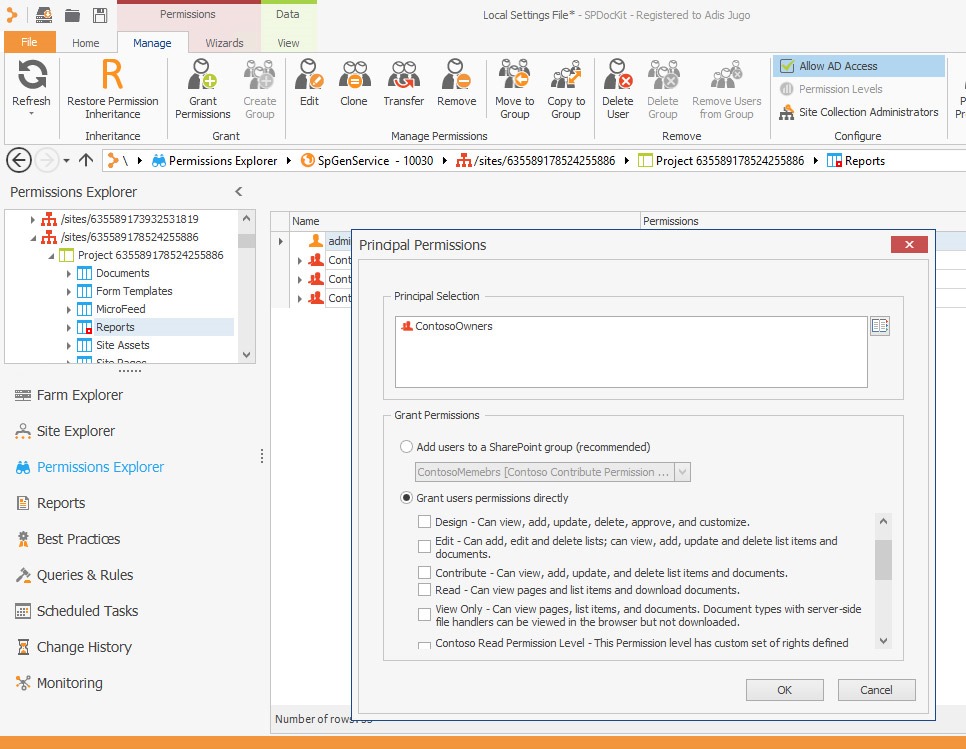
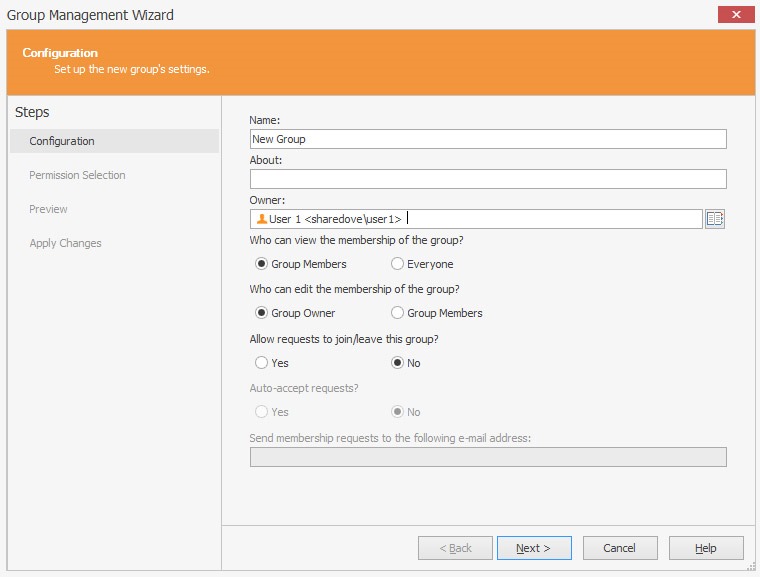
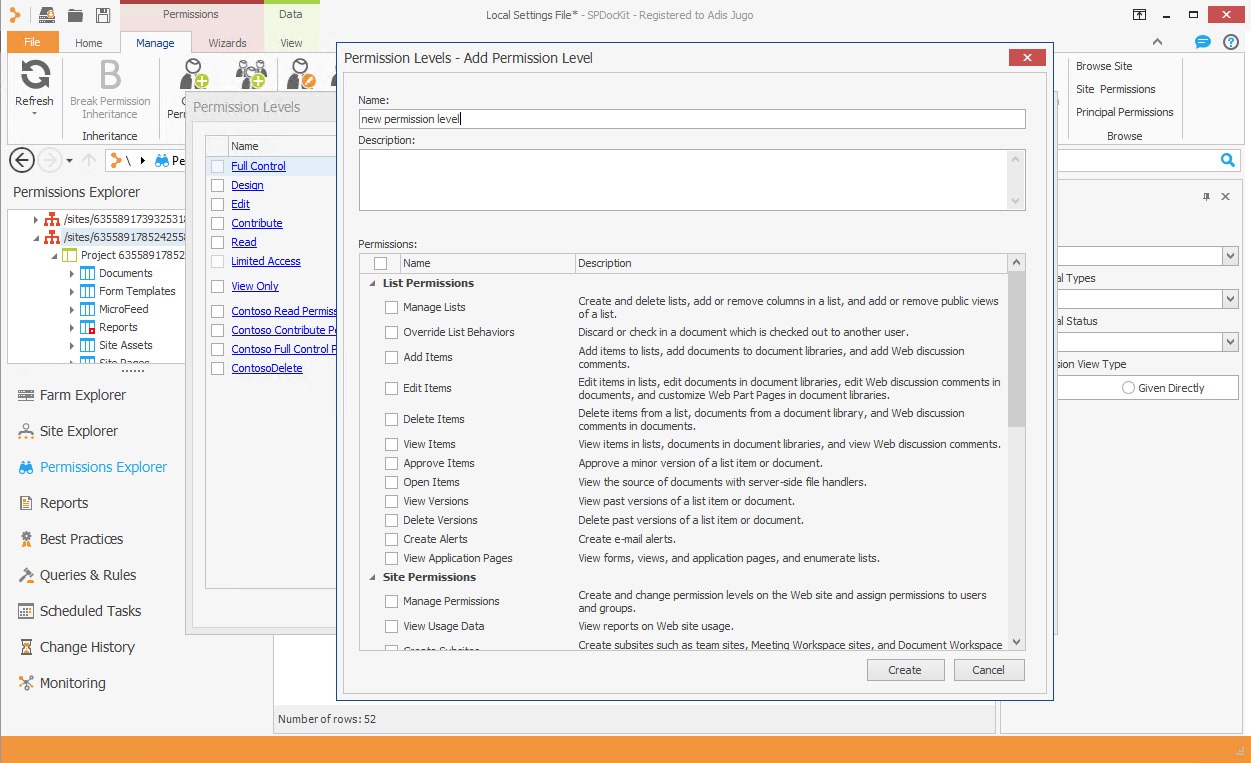
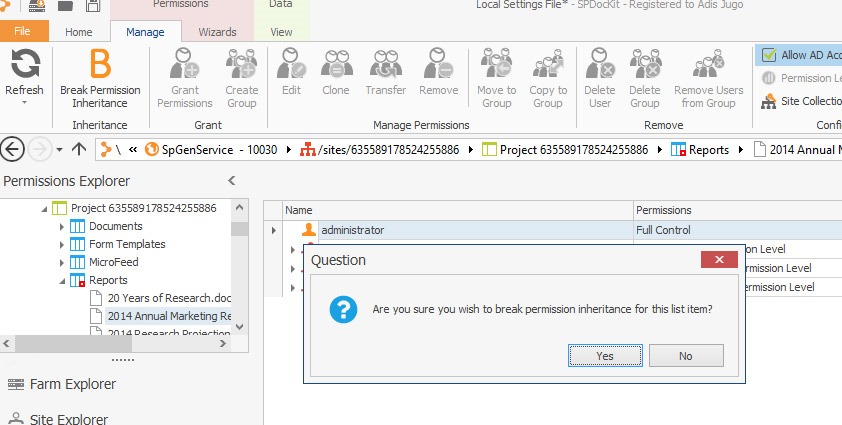
Everyday operations are one click away, including detecting securable objects with unique permissions (broken permissions inheritance); breaking and restoring permissions; creating, editing, and deleting SharePoint Groups and Permission levels; and managing group memberships. This easy access significantly reduces the time needed to perform those repetitive tasks compared to the standard user interface.
While browsing through the site structure, administrators can easily see who has permissions on the currently selected object. Furthermore, they can filter those permissions based on the principal’s status (enabled or disabled), type (SharePoint Group, AD Group, or user), and—in an interesting feature—history. Each time SPDocKit loads the farm information, it writes the information in the background database. Administrators can then use it as a kind of “wayback machine” for permissions.
In addition to browsing and exploring permissions, administrators can define permissions settings on the site collection level for primary and secondary site collection administrators, members of the administrators group, as well as for SharePoint Groups and Permission levels.
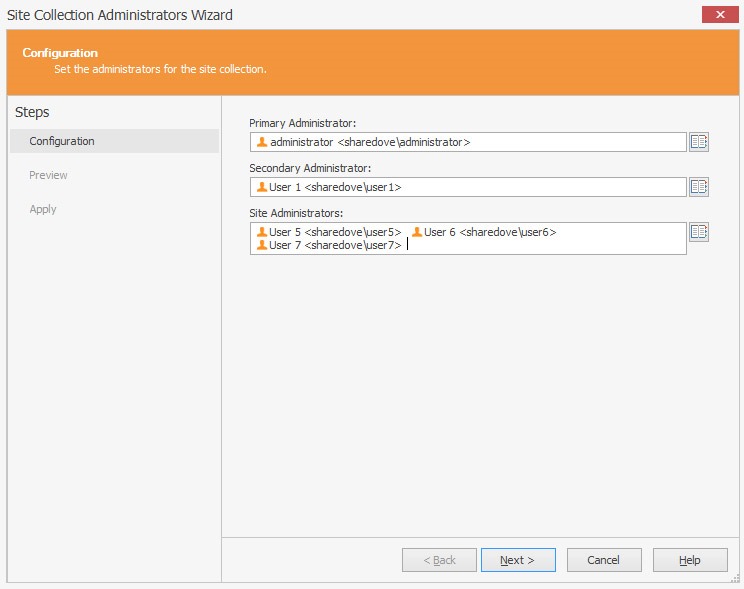
Setting the site collection administrators
While drilling down through the hierarchy, administrators can break and restore permission inheritance at any location and grant or revoke permissions for the currently selected object.
All these features help administrators significantly speed up their work with permissions.
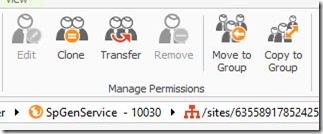
Besides simply speeding up repetitive everyday tasks, SPDocKit offers some useful automations for tasks that would normally require a lot of clicking or scripting. If you look at the Manage Permissions ribbon, you will see “Edit,” “Clone,” “Transfer,” “Remove,” “Move to Group,” and “Copy to group” icons.
While it is pretty clear what “Edit” and “Remove” do (change permission levels or revoke permissions for a principal completely), the other four icons are particularly interesting.
Although the SharePoint 2013 “Share” icon allows users to quickly share content with another users, it creates a lot of (sometimes unnecessary) item level permissions when it would be much better to simply add users in the appropriate SharePoint groups. With SPDocKit, administrators can clean that mess up pretty easily by selecting the “loose” principals on objects with broken permission inheritances and copying and moving them to the appropriate SharePoint groups—all with one click.
“Clone” and “Transfer” offer more interesting functions. Administrators often face requirements such as “User X needs to have exactly the same permissions as User Y” or “User Z is being transferred to another division and User W is taking his place.” SPDocKit’s “Clone” and “Transfer” capabilities do exactly that—they give new users the same rights an existing user has or transfer the rights to that user and revoke them from the original user. That comes in pretty handy in day-to-day work.
Of course, as you would expect for a tool of this caliber, SPDocKit allows administrators to get information about each user in the site collection (e.g., where does the user come from and what are his or her group memberships for SharePoint and AD groups). Overall, this is a powerful toolset that helps administrators perform permissions-related tasks.